
[ad_1]
Still a devoted WinRar person? You must replace your software program proper now, particularly in the event you’ve received cryptocurrency. A zero-day vulnerability in WinRar has been permitting hackers to interrupt into buying and selling accounts, and so they’ve been actively working this exploit since April. The identical vulnerability may very well be used to put in different varieties of malware in your system as effectively,.
The means it really works: You open a malicious zip file in WinRAR, which is your default program for all compressed file codecs in your PC (after you’ve put in WinRar, after all). It’s filled with seemingly harmless paperwork—PDFs, textual content recordsdata, JPG photos. You double click on on one to open it, which it does. But unbeknownst to you, WinRAR was additionally tricked into loading a script within the background, which installs malware that lets attackers steal cash from brokerage accounts.
As reported by Bleeping Computer, WinRAR model 6.23 fixes this challenge together with others, like a flaw that permits instructions to be executed in the event you open sure sorts of rar recordsdata. (That is, rar recordsdata created in a selected strategy to exploit that flaw.) It launched on August 2 and must be obtainable to all WinRAR customers.
Group-IB (through Bleeping Computer)
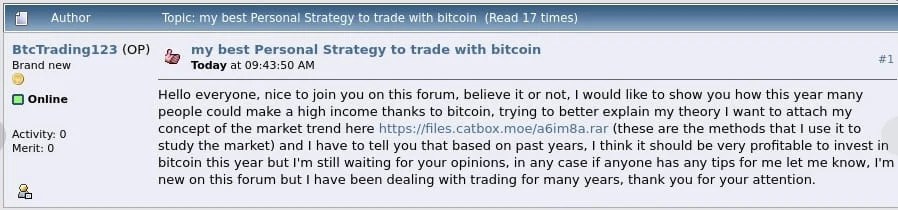
Cybersecurity firm Group-IB discovered this vulnerability (filed as CVE-2023-38831) whereas monitoring the unfold of the DarkMe malware household, which has been linked beforehand to monetary assaults. The tainted zip recordsdata, which had been posted on boards for cryptocurrency and inventory buying and selling, contained DarkMe and different malware households like GuLoader and Remcos. The latter two households permit extra malware to be downloaded and put in in your PC, in addition to giving the power to run any command, report keystrokes, display seize, handle recordsdata, and extra to the attacker. (For deeper technical particulars, take a look at Bleeping Computer’s rundown of the exploit.)
At the time of Group-IB’s report, 130 merchants have been confirmed as contaminated. The zip recordsdata had been shared on at the very least eight boards, all beneath the guise of serving to others enhance their revenue. Currently, the total sufferer rely and quantity of monetary damages are usually not but identified.
If nothing else, this WinRAR assault is yet one more reminder that the previous safety tip of by no means downloading unusual recordsdata off the web (a lot much less opening) them nonetheless stays true. It may also be seen as extra incentive to improve to Windows 11, which is able to quickly natively support compressed file codecs like rar, 7-Zip, and gz—no want for third-party software program.
[adinserter block=”4″]
[ad_2]
Source link